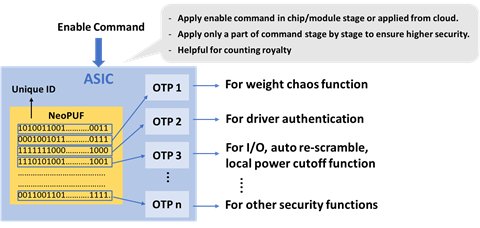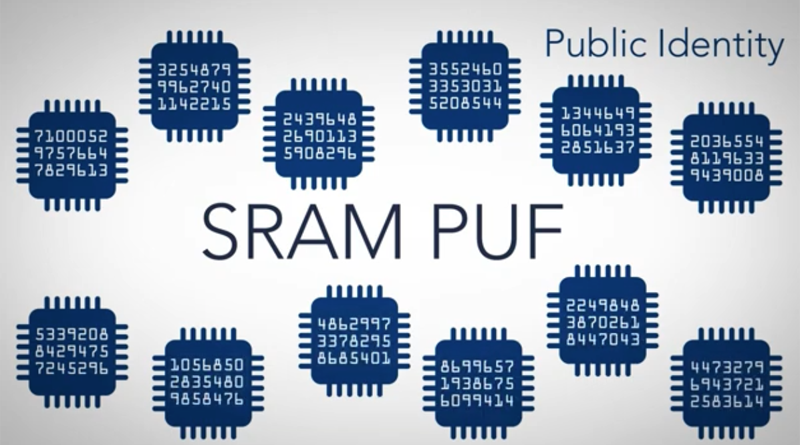
Dispositivos IoT con huella digital de silicio gracias a la función física no clonable aplicada en el proyecto Instet • CASADOMO
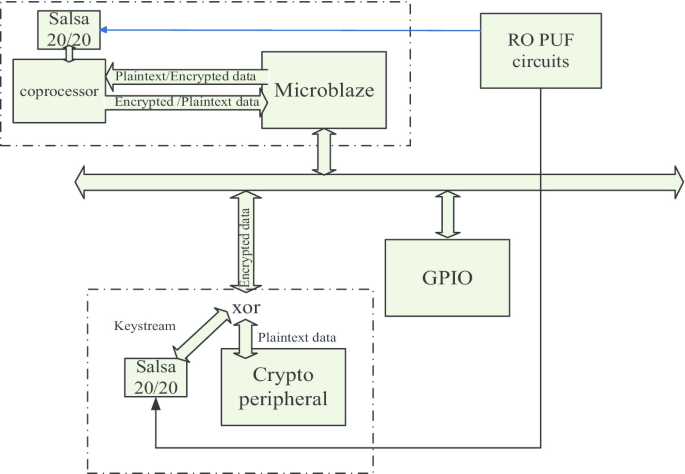
A PUF-based cryptographic security solution for IoT systems on chip | EURASIP Journal on Wireless Communications and Networking | Full Text